Tor vs VPN: Which is Better? Anonymous Browsing in 2019
Updated on July 13, 2021: From now on, traffic filtering, malware protection, and suspicious DNS activity blocking are available as a part of the separate DNS Firewall app.
Looking into ways to avoid monitoring and stay anonymous online? Tor browser and VPN services are the most popular online privacy tools for this. Though to many users they may seem very much alike, which is true to some extent, these two technologies have significant differences. How Tor and VPNs work, is Tor the same as a VPN, what their peculiarities are, who wins in the Tor vs VPN battle, and which one to choose: Tor or VPN? VPN Unlimited team has prepared answers to these questions. Take them away!
- What is Tor?
- How does Tor work?
- Tor browser: pros & cons
- Can I be traced on Tor?
- What is VPN and how does VPN work?
- Should you use a VPN: VPN pros & cons
- Tor vs VPN: which one to choose to stay anonymous?
- Bottom line on anonymous browsing with Tor and VPN
What is Tor?
Tor stands for The Onion Router. It refers both to the network of computers for managing Tor connections and the software you install to run Tor.
The Tor technology disguises your identity by encrypting and directing your traffic via Tor servers. As a result, the party on the other end of your connection can’t trace the traffic back to you.
Tor Browser History
Initially, Tor was a network of servers created by the U.S. Navy to conceal their IP addresses and protect sensitive data during reconnaissance and intel gathering. When the military switched to higher anonymity VPN services, Tor became a legal open source software, available for download on the Tor website.

As the “onion” part of the name implies, there are a number of layers created by Tor to make you anonymous. Tor doesn’t rely on a specific proxy server for data processing, it is a multi-proxy network. Its numerous servers are scattered around the world and are maintained by individual volunteers. As the servers don’t belong to a single company or organization, it’s quite difficult to intercept or trace Tor connections.
How does Tor work?
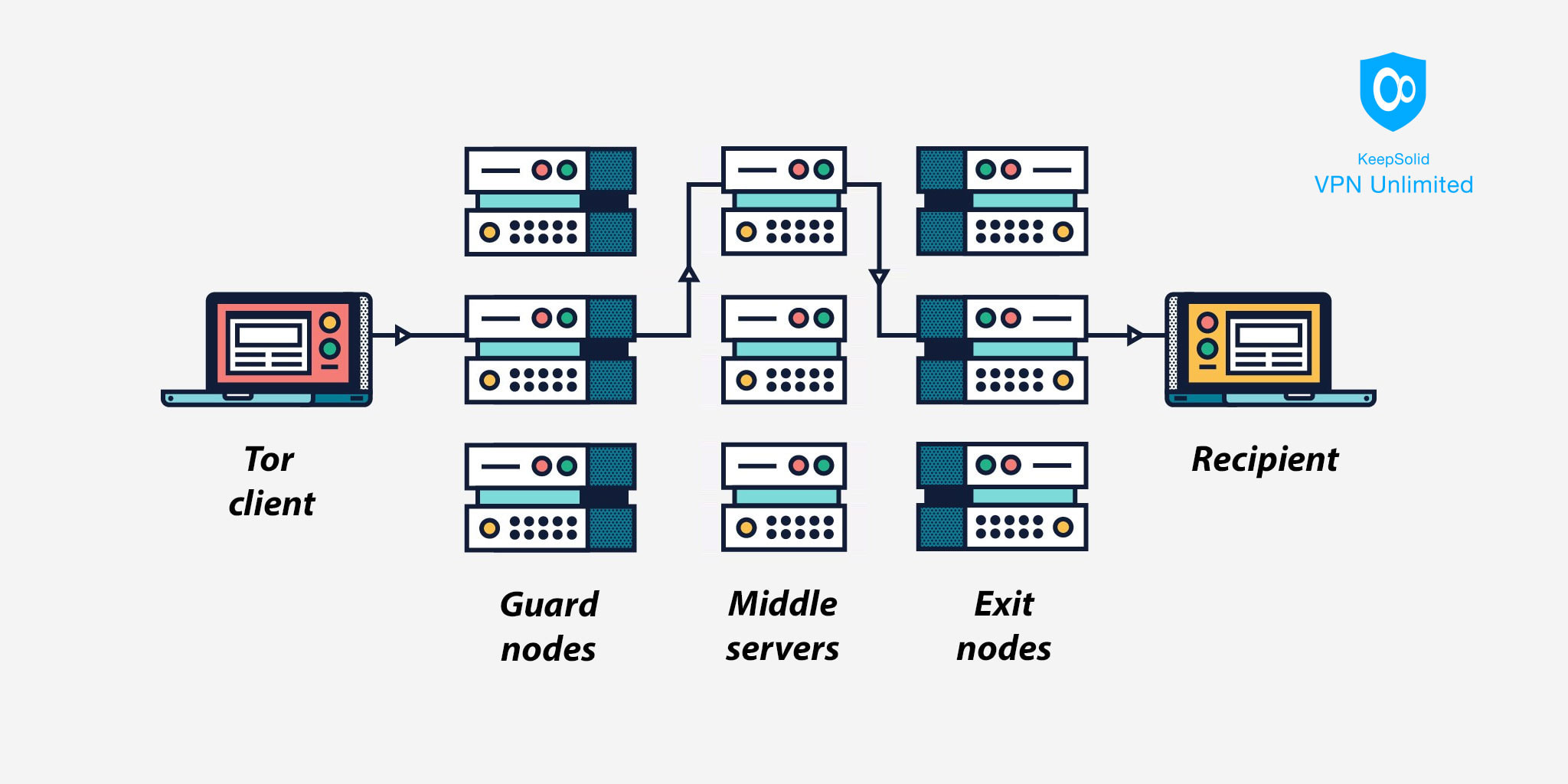
When your computer sends a message using the Tor network, here’s what happens:
- The Tor software on your device selects 3 random Tor servers and builds a path between them. These servers are called a guard node, a middle server, and an exit node.
At this stage, your message undergoes multiple encryption process – Tor enciphers it 3 times for each of the 3 different nodes. - Once your message is encrypted, Tor sends it to the first server, or the guard node. It removes one layer of encryption before passing your message to the next server.
Though the guard node can see your IP address, it is unable to read the encrypted message because of the 2 layers of encryption left. - The process repeats. The middle server takes off the second layer and passes the message to the exit node. As you may guess, similarly to the first server, it can’t read the contents of your message as well.
- The exit node peels off the final layer and can read the decrypted message. However, it is unable to identify your IP address, so the sender remains unknown. This last server then passes the message to the recipient.
Tor browser: pros & cons
Let’s explore Tor browser pros and cons in detail. Surfing the web with Tor provides the following advantages:
- The multiple encryption process makes you anonymous.
- Tor is free and easy to use.
- It’s difficult to shut down, as Tor network is made up of thousands of servers maintained by individual volunteers. Its distributed network has no central office or main server to attack.
- You may be able to access certain geo-blocked content.
But even Tor has its cons, including:
- Complexity of encryption considerably slows down your internet connection.
- To get an IP address of a specific country, you’ll have to connect and reconnect multiple times till you randomly stumble upon a server in the required location.
- The message content can be intercepted by exit nodes.
- With Tor network being run by volunteers, no one can guarantee proper maintenance and timely upgrades of the network. Some servers may be old and slow and provide weak internet connection. Besides, with so many volunteers there is always a risk of the human factor.
- The Tor browser only protects the traffic that goes through the Tor connection and doesn’t extend to other apps on your device.
Can I be traced on Tor?
Even with all the Tor’s complex technology, it doesn’t eliminate privacy risks completely. Your message is visible to the organization or person that operate the exit node. Its security entirely depends on the owner, as anyone can set up a node.
Besides, if an organization operates a large number of Tor servers, it may even deanonymize users. How? By owning both guard and exit nodes, thus getting access to the user’s identity and their message.
So, the answer is – Yes, you can be traced on the Tor. But how to browse anonymously, without these risks? Read on to find it out!
What is VPN and how does VPN work?
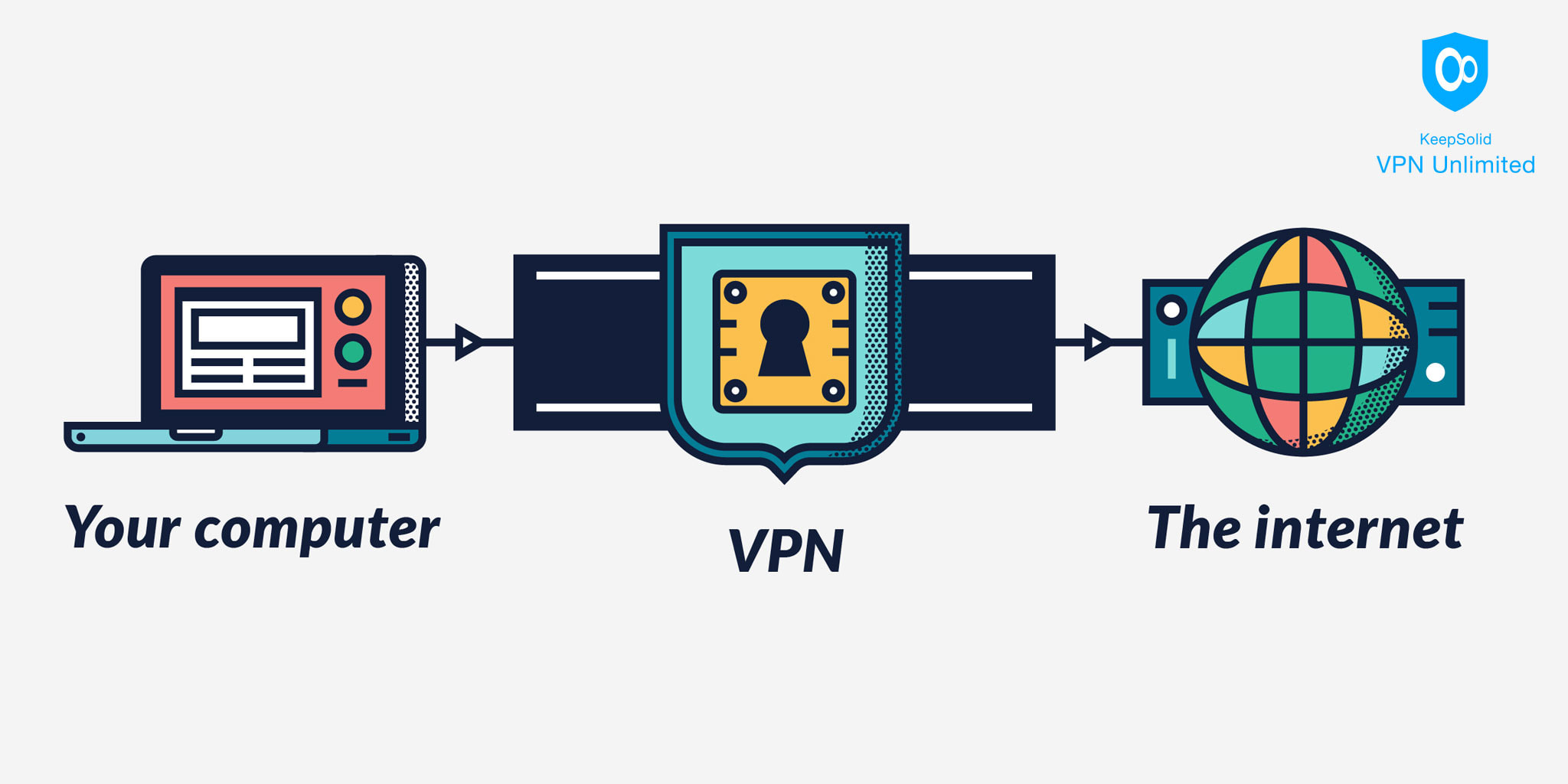
VPN, or Virtual Private network, is the technology that encrypts your data and directs traffic via an intermediary VPN server. VPN services provide a number of servers in various locations to choose from, so you can get whatever country IP address you want.
Top-notch VPN software like VPN Unlimited employs reliable, military-grade 256-bit encryption technique. This cypher is impossible to brute-force, so you stay anonymous and all your data is completely secure.
Information sent from your device passes through a remote VPN server before reaching its destination. Likewise, the traffic sent to your computer passes through the same encrypted tunnel before reaching your device.
VPN makes it impossible for your ISP or any third parties to peer into your traffic, making you completely anonymous online and protecting all your private data.
Should you use a VPN: VPN pros & cons
As opposed to Tor, with a reputable VPN it’s easy to tell who runs the servers, so the end-user can be sure about the quality of service. Other advantages of using a VPN service include:
- Faster connection speeds compared to Tor, due to the less complicated routing scheme.
- Encryption of all your internet traffic, not just the browsing data.
- Accountability – it is possible to tell who the servers belong to.
- Access to geo-restricted content – you can easily get an IP address of the location where the content you’re looking for is available.
- Compatibility with most popular devices and even routers.
- Customer support available 24/7 to answer your questions and solve any technical issues.
- VPN Unlimited offers advanced capabilities, such as special servers for safe torrent download and for unblocking ESPN, Hulu, and other streaming services.
Though a VPN service provides lots of benefits, there are still some concerns left:
- Your data passes through fewer servers and you entrust your information to a single service provider.
- Depending on the providers, policies, and jurisdiction, some VPNs collect user logs. Moreover, a recent research shows that a number of VPN providers are secretly owned by firms from China, where privacy laws are quite lax.
- A good VPN software is not free, as providers need to maintain a network of servers, keep the software and hardware upgraded, etc.
All the mentioned issues can be easily addressed just by choosing a trustworthy provider. For instance, VPN Unlimited is just the perfect security and privacy solution for you. With its transparent privacy policy and affordable VPN plans, you can enjoy all the benefits of an advanced VPN without any privacy concerns. Download and try it out for free right now!
Tor vs VPN: which one to choose to stay anonymous?
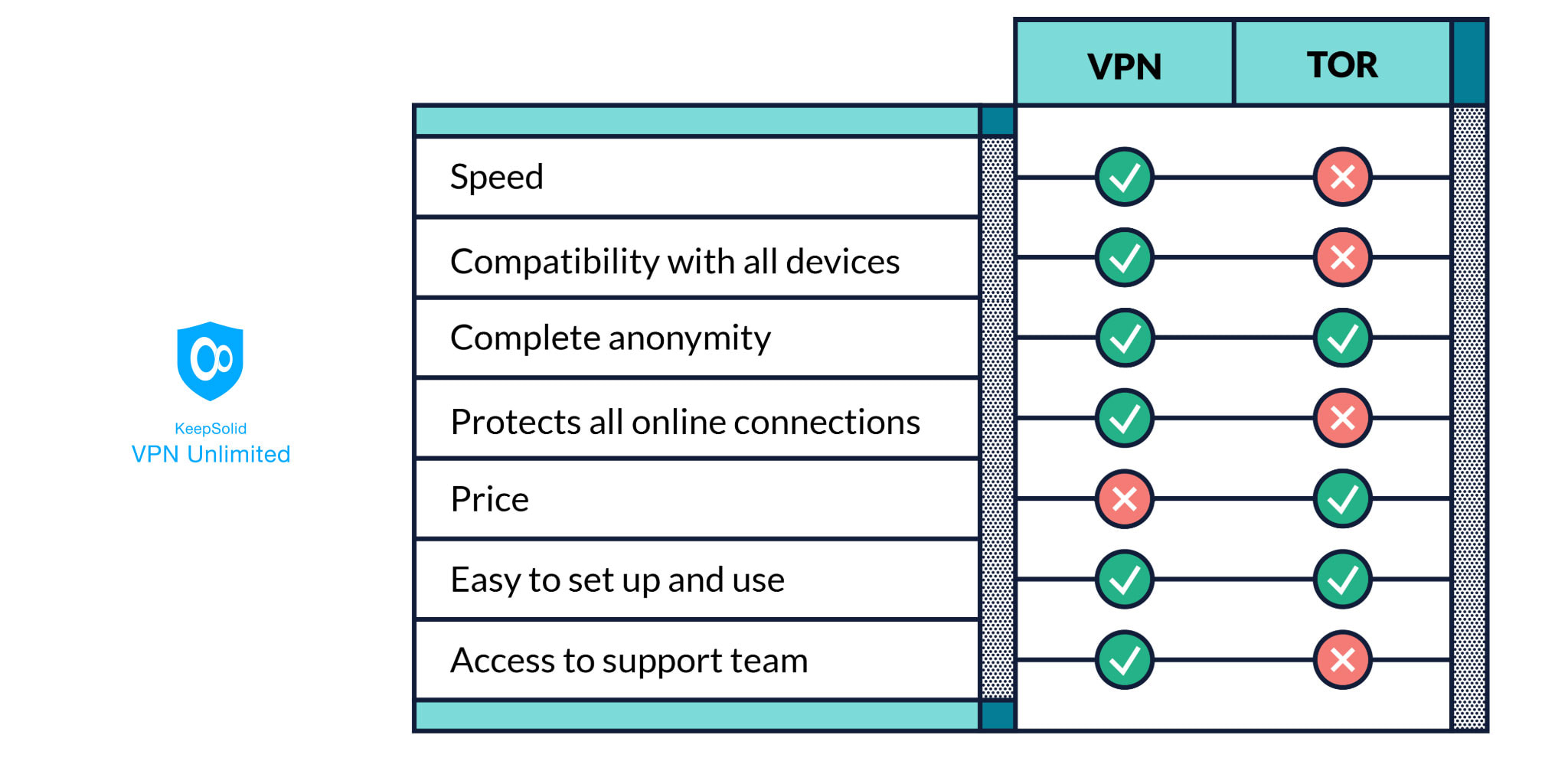
To make the choice easier for you, we’ve summarized the pros and cons of Tor and VPNs in the chart below.
Bottom line on anonymous browsing with Tor or VPN
We hope that now you can tell which is better – Tor or VPN. The answer is – a trustworthy VPN! It offers more accountability, better speed and protection, and other hefty benefits. Download VPN Unlimited to protect all your traffic and enjoy completely anonymous browsing wherever you are!