- Launch VPN Unlimited
- Tap on the Menu icon in the upper left corner of the app
- Then go to Settings
- Select the Protocols tab
- Choose the L2TP/IPSec option to turn on the L2TP protocol
What is L2TP VPN Protocol?
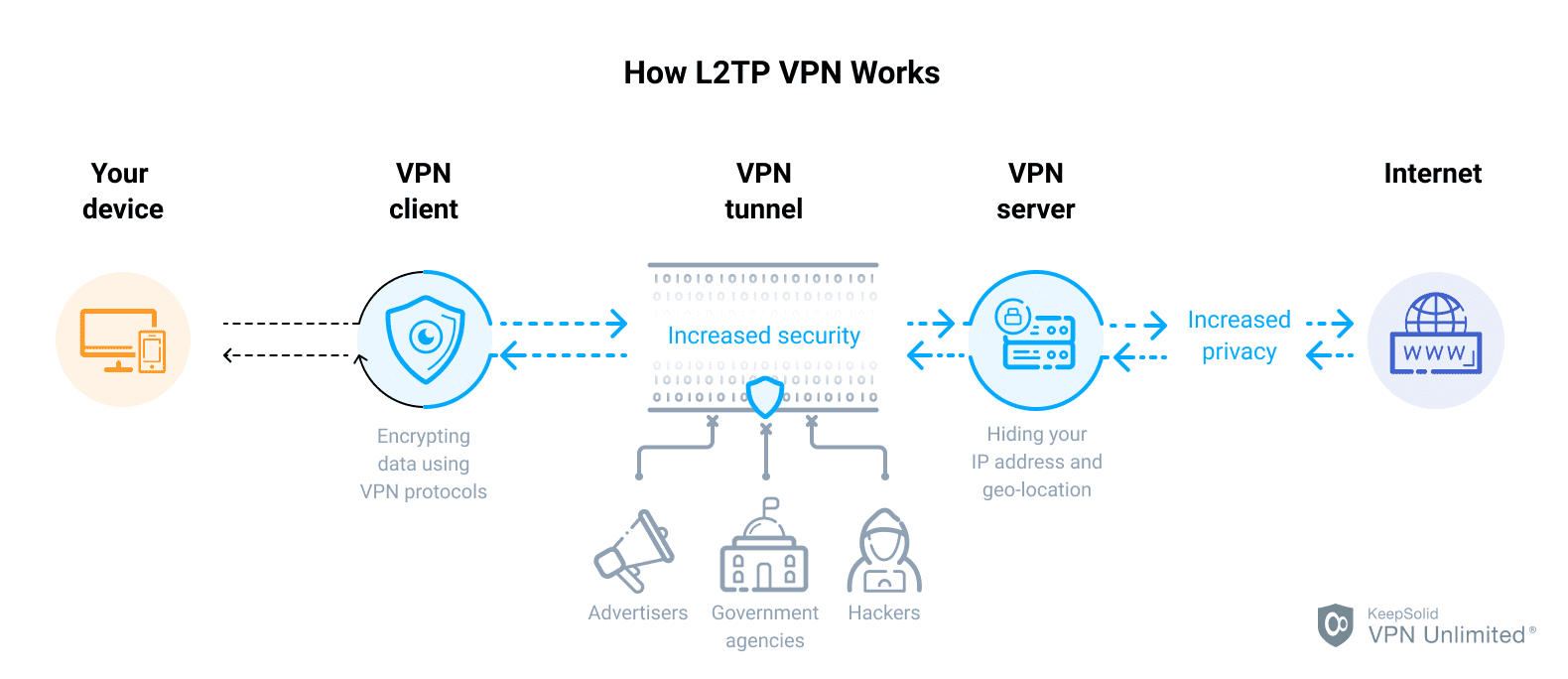
L2TP or Layer 2 Tunneling Protocol is an extension to the PPP protocol that merges the best features of two other tunneling protocols PPTP (Point-to-Point Tunneling Protocol) and L2F (Layer 2 Forwarding Protocol) and is used to support virtual private networks (VPNs).
As this protocol does not provide confidentiality or strong authentication by itself, Layer 2 Tunneling Protocol is often implemented along with the IPSec tunneling protocol to secure the connection. Go on reading to learn more about the combination of these two protocols, generally known as L2TP/IPsec.
Benefits of L2TP VPN Tunneling Protocol
Security
The L2TP VPN Protocol is considered to be the most secure among the others. It prevents data from being altered while moving between the sender and receiver. It also encrypts the authentication process making it more difficult for someone to interfere.
Speed
Depending on the L2TP/IPsec server configuration, L2TP/IPsec can be almost as fast as a regular non-encrypted connection to the server. Speed-wise - it can provide a 100 Mbps broadband or come close in most cases.
Compatible platforms
As with any open tunneling protocol, L2TP is widely supported on a variety of target platforms, including mobile devices. Even better, with multiple projects supporting L2TP on Linux or BSD platforms, there is no need to make expensive hardware investments to support an L2TP deployment on your network.
L2TP and IPSec synergy
Since L2TP doesn't provide any authentication or encryption mechanisms directly, both of which are key features of a VPN, L2TP is usually paired with IPSec to provide encryption of user and control packets within the L2TP tunnel. IPsec is a very flexible tunneling protocol for end-to-end security that authenticates and encrypts each individual IP packet in a given communication.
How L2TP and IPsec Work Together
L2TP was first proposed in 1999 as an upgrade to both L2F and PPTP. Because L2TP can’t provide strong encryption or authentication, another tunneling protocol called IPsec is used in conjunction with L2TP.
L2TP/IPsec encapsulates data twice, which can slow down the connection. However, the protocol makes this up by providing the encryption/decryption process in the kernel and allowing multi-threading that is not possible in the OpenVPN protocol. This fact, theoretically, makes L2TP together with IPsec faster than OpenVPN and safer than PPTP.
L2TP/IPsec is just as easy and quick to set up as PPTP but is much more secure. Yet, because the L2TP protocol uses UDP port 500, there are chances that the VPN connection will be detected and blocked by some firewalls.
L2TP Security and Speed
Why L2TP/IPsec is popular:
- Secure connection - works with AES and 3DES encryption algorithms (256-bit key)
- Reliable link establishment - uses UDP Port 1701, Port 500, and Port 4500
- Safe tunneling protocol - employs top-tier encryption and encapsulation
L2TP employs IPSec for extra security, which offers better data protection than PPTP. Also, data transferred via L2TP cannot be altered along the way while traveling from the sender to the receiver. This tunneling protocol encrypts even the authentication process itself, making it more difficult for third parties to force their way in and see your transmission.
With UDP encapsulating data, L2TP is also easier and faster to set up with most firewalls. L2TP is a good option for you if security is more important to your VPN than speed.
Communicate wherever you are with VPN Unlimited!
Message your friends with our best VPN tunneling protocols and don’t let any obstacles restrict your communication. Enjoy all the advantages of a secure L2TP connection!
L2TP VPN Protocols Advantages and Disadvantages
Advantages
- Uses AES-256 bit encryption, thus considered secure and safe
- Supports a wide range of desktop and mobile operating systems
- Very easy to configure
- Offers better data protection than PPTP
Disadvantages
- Uses UDP port 500 that can cause blocks from some firewalls
- Slightly slower than IPSec IKEv2 because of its double encapsulation
What Other Protocols VPN Unlimited Supports
Different situations require different approaches. And when you know which VPN protocol in which situation you need, you receive the best experience online. That’s why the set of available VPN protocols is a great benefit of VPN Unlimited. It makes our client more flexible and provides a possibility to choose from a number of options. VPN Unlimited supports the following VPN tunneling protocols on various devices:
“OpenVPN” is a registered trademark of OpenVPN Inc.
FAQ About VPN and L2TP Protocol
Download VPN Unlimited for free right now!
Our reliable VPN client and the fastest VPN protocols are at your disposal to provide you with complete data security and confidentiality at all times.