Demystifying Private Browsing: Does It Leave a Trace on WiFi?

Private browsing, often referred to as Incognito mode or Privacy mode, is a feature offered by most modern web browsers. It aims to provide users with a level of anonymity by preventing the browser from storing local data such as browsing history, cookies, and temporary files. While private browsing is widely used, there are common misconceptions about its effectiveness in maintaining privacy, especially concerning its visibility on WiFi networks. This article explores the intricacies of private browsing and investigates whether it leaves any traces on WiFi.
Understanding Private Browsing
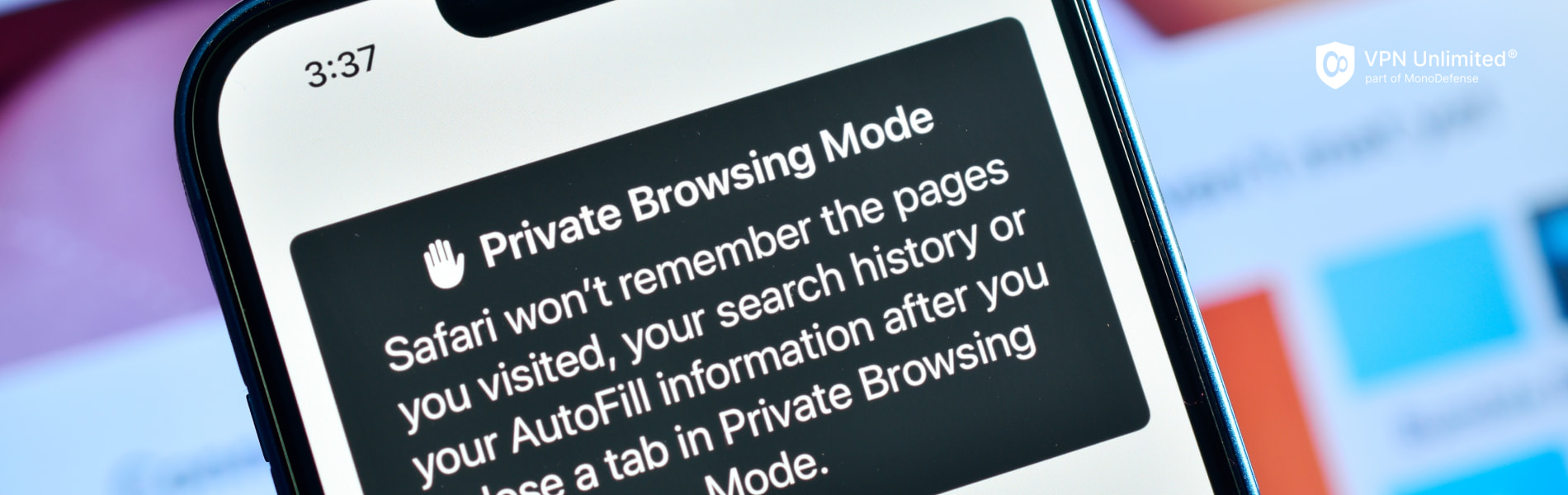
In various browsers, private browsing goes by different names. Google Chrome labels it as "Incognito mode," Mozilla Firefox uses "Private Browsing," and Safari refers to it simply as "Private mode." Despite the nomenclature differences, the fundamental purpose remains consistent — to enable users to explore the internet without leaving a digital trail on their devices.
The mechanism behind private browsing involves session isolation and sophisticated cookie management. When a user initiates a private browsing session, the browser creates a separate environment that operates independently of the regular session. Any actions performed within this private mode are confined to the isolated session, ensuring that data generated during the session, such as visited websites or search queries, does not get stored locally.
Furthermore, private browsing typically employs a different approach to handling cookies. Cookies, which are small pieces of data stored by websites on a user's device, play a crucial role in personalizing the browsing experience. In private browsing mode, these cookies are either not stored at all or are deleted upon the session's conclusion. This ensures that any potential identifiers or tracking information associated with cookies are not retained after the user exits the private browsing session.
The Basics of WiFi Network Monitoring

WiFi networks operate by transmitting data wirelessly through radio waves. Devices, such as laptops, smartphones, or smart home gadgets, connect to the network, allowing the seamless exchange of information. This wireless communication relies on routers that facilitate the flow of data packets between devices, forming the backbone of our modern internet connectivity.
WiFi network monitoring involves the use of tools capable of intercepting and analyzing data packets traveling across the network. One prominent method is packet sniffing, a technique where monitoring tools capture and inspect the data packets exchanged between devices. This process allows administrators or individuals with access to the network to examine the contents of the transmitted data, including unencrypted information.
Does Private Browsing Show Up on WiFi?

The question of whether private browsing leaves a trace on WiFi networks involves a nuanced exploration of its impact on both local device history and network logs. To dissect this, it's crucial to clarify the scope, distinguishing between the effects on the user's device and any potential traces within the broader network environment.
Private browsing primarily targets the local device, aiming to leave no discernible trace in terms of browsing history, downloaded files, or stored cookies once the session concludes. The primary goal is to enhance privacy for the individual user by preventing others with physical access to the device from accessing a detailed record of their online activities.
Moving beyond the local device, the impact of private browsing on WiFi networks requires consideration of router logs and network monitoring tools. These tools can capture data packets exchanged between the device and the network, potentially revealing information about visited websites or data transfers.
The investigation into whether private browsing leaves noticeable traces on WiFi networks involves understanding how routers log and store data. While private browsing is designed to minimize local traces, the broader network environment may still retain information about the communication between the device and the internet. In the subsequent sections, we will delve deeper into the nuances of private browsing's interaction with network-level monitoring tools and the potential traces it may leave within the WiFi network logs.
Privacy Risks and Limitations
Various factors contribute to the nuanced landscape of online privacy, and private browsing is not immune to certain privacy risks. For instance, if a user forgets to initiate a private browsing session or switches to regular browsing unintentionally, traces may be left on the device. Additionally, some browser extensions or plugins may still collect data irrespective of the browsing mode.
Furthermore, private browsing does not encrypt the data exchanged between the device and the websites visited. As a result, Internet Service Providers (ISPs) or network administrators could potentially intercept and inspect this unencrypted data, compromising the user's privacy. These scenarios underscore the importance of users maintaining awareness of the limitations of private browsing in specific contexts.
To address the gaps in private browsing, especially concerning the potential interception of data during transmission, the implementation of encryption and secure connections becomes paramount. Users are encouraged to prioritize websites that use HTTPS, ensuring that data exchanged between the device and the website is encrypted, safeguarding it from prying eyes during transit.
Moreover, employing Virtual Private Networks (VPNs) can add an extra layer of protection. VPNs encrypt all internet traffic, not just the browsing session, masking the user's IP address and enhancing overall online privacy.
In conclusion, understanding the inherent limitations and potential risks associated with private browsing is integral to forming a comprehensive strategy for online privacy. While private browsing serves as a valuable tool, users should supplement it with encryption measures and secure connections to bolster their defenses against potential privacy breaches. The next section will delve into best practices for securing WiFi networks, providing users with additional layers of protection in their quest for a secure and private online experience.
WiFi Network Security Best Practices
Securing WiFi Networks with Strong Passwords
Securing your WiFi network begins with a robust password. A strong password acts as the first line of defense against unauthorized access. It should be complex, incorporating a mix of uppercase and lowercase letters, numbers, and symbols. Avoid using easily guessable information, such as names or birthdays, to enhance the security of your WiFi network.
Use of WPA3 Encryption for Enhanced Security
To fortify your WiFi network against potential breaches, consider upgrading to WPA3 (Wi-Fi Protected Access 3), the latest and most secure encryption protocol for wireless networks. WPA3 enhances the protection of your network by providing stronger encryption algorithms and resistance against various attacks, including those attempting to guess passwords.
Regularly Update Router Firmware and Change Default Settings
Keeping your router's firmware up to date is crucial for addressing security vulnerabilities and ensuring optimal performance. Manufacturers regularly release updates to patch potential weaknesses. Additionally, changing default settings, such as default passwords and network names (SSIDs), helps thwart common cyber threats that exploit standardized configurations. Regularly reviewing and updating these settings contributes significantly to a more secure WiFi environment.